3253de73ec7e09265a013c1cfdd5730f2190dfb7
* web: Add InvalidationFlow to Radius Provider dialogues
## What
- Bugfix: adds the InvalidationFlow to the Radius Provider dialogues
- Repairs: `{"invalidation_flow":["This field is required."]}` message, which was *not* propagated
to the Notification.
- Nitpick: Pretties `?foo=${true}` expressions: `s/\?([^=]+)=\$\{true\}/\1/`
## Note
Yes, I know I'm going to have to do more magic when we harmonize the forms, and no, I didn't add the
Property Mappings to the wizard, and yes, I know I'm going to have pain with the *new* version of
the wizard. But this is a serious bug; you can't make Radius servers with *either* of the current
dialogues at the moment.
* This (temporary) change is needed to prevent the unit tests from failing.
\# What
\# Why
\# How
\# Designs
\# Test Steps
\# Other Notes
* Revert "This (temporary) change is needed to prevent the unit tests from failing."
This reverts commit dddde09be5.
* web: Update to OpenAPI 7.11.
This commit updates our Makefile to generate the Typescript api using OpenAPI 7.11, and updates
names (mostly of enum targets) in our product to correspond to the changes in how OpenAPI generates
enum source names.
1. Replaced `ProviderModelEnum.` (note terminal period) with `ProviderModelEnum.AuthentikProvider`.
For example:
```
- ProviderModelEnum.SamlSamlprovider
+ ProviderModelEnum.AuthentikProvidersSamlSamlprovider
```
2. Replaced `RbacPermissionsAssignedByUsersListModelEnum.` (note terminal period) with
`RbacPermissionsAssignedByUsersListModelEnum.Authentik`. For example:
```
- RbacPermissionsAssignedByUsersListModelEnum.ProvidersLdapLdapprovider.toString(),
+ RbacPermissionsAssignedByUsersListModelEnum.AuthentikProvidersLdapLdapprovider.toString(),
```
3. Replaced `SyncObjectModelEnum.` (note terminal period) with
`SyncObjectModelEnum.AuthentikCoreModels`. For example:
```
- model=${SyncObjectModelEnum.Group}
+ model=${SyncObjectModelEnum.AuthentikCoreModelsGroup}
```
4. Replaced `SignatureAlgorithmEnum._` (note terminal symbols) with
`SignatureAlgorithmEnum.HttpWwwW3Org`. For example:
```
- ["ECDSA-SHA256", SignatureAlgorithmEnum._200104XmldsigMoreecdsaSha256],
+ ["ECDSA-SHA256", SignatureAlgorithmEnum.HttpWwwW3Org200104XmldsigMoreecdsaSha256],
```
5. Replaced `DigestAlgorithmEnum._` (note terminal symbols) with `DigestAlgorithmEnum.HttpWwwW3Org`.
For example:
```
- ["SHA256", DigestAlgorithmEnum._200104Xmlencsha256, true],
+ ["SHA256", DigestAlgorithmEnum.HttpWwwW3Org200104Xmlencsha256, true],
```
6. Replaced `NameIdPolicyEnum._` (note terminal symbols) with
`NameIdPolicyEnum.UrnOasisNamesTcSaml`. This one is trickier than the others: If you look
closely, you'll see that how OpenAPI generates the names has changed, with `nameid` now being
`Nameid`, and `FormatemailAddress` now being `FormatEmailAddress`.
```
- value=${NameIdPolicyEnum._11nameidFormatemailAddress}
+ value=${NameIdPolicyEnum.UrnOasisNamesTcSaml11NameidFormatEmailAddress}
```
# How
After determining how the enum prefixes had changed, I just ran six of these, testing after each
step to ensure that `npm run lint:types` had fewer errors than the previous run, until the product
built without type errors.
``` sh
$ perl -pi.bak -e 's/DigestAlgorithmEnum\._/DigestAlgorithmEnum.HttpWwwW3Org/' $(rg -l 'DigestAlgorithmEnum\.' src/)
```
# Testing
You can validate that these items have changed by finding the prefixes in the source code and
assuring yourself that every option, checkbox, or radio associated with them is populated correctly.
# User documentation changes required.
None.
# Developer documentation changes required.
None.
What is authentik?
authentik is an open-source Identity Provider that emphasizes flexibility and versatility, with support for a wide set of protocols.
Our enterprise offer can also be used as a self-hosted replacement for large-scale deployments of Okta/Auth0, Entra ID, Ping Identity, or other legacy IdPs for employees and B2B2C use.
Installation
For small/test setups it is recommended to use Docker Compose; refer to the documentation.
For bigger setups, there is a Helm Chart here. This is documented here.
Screenshots
| Light | Dark |
|---|---|
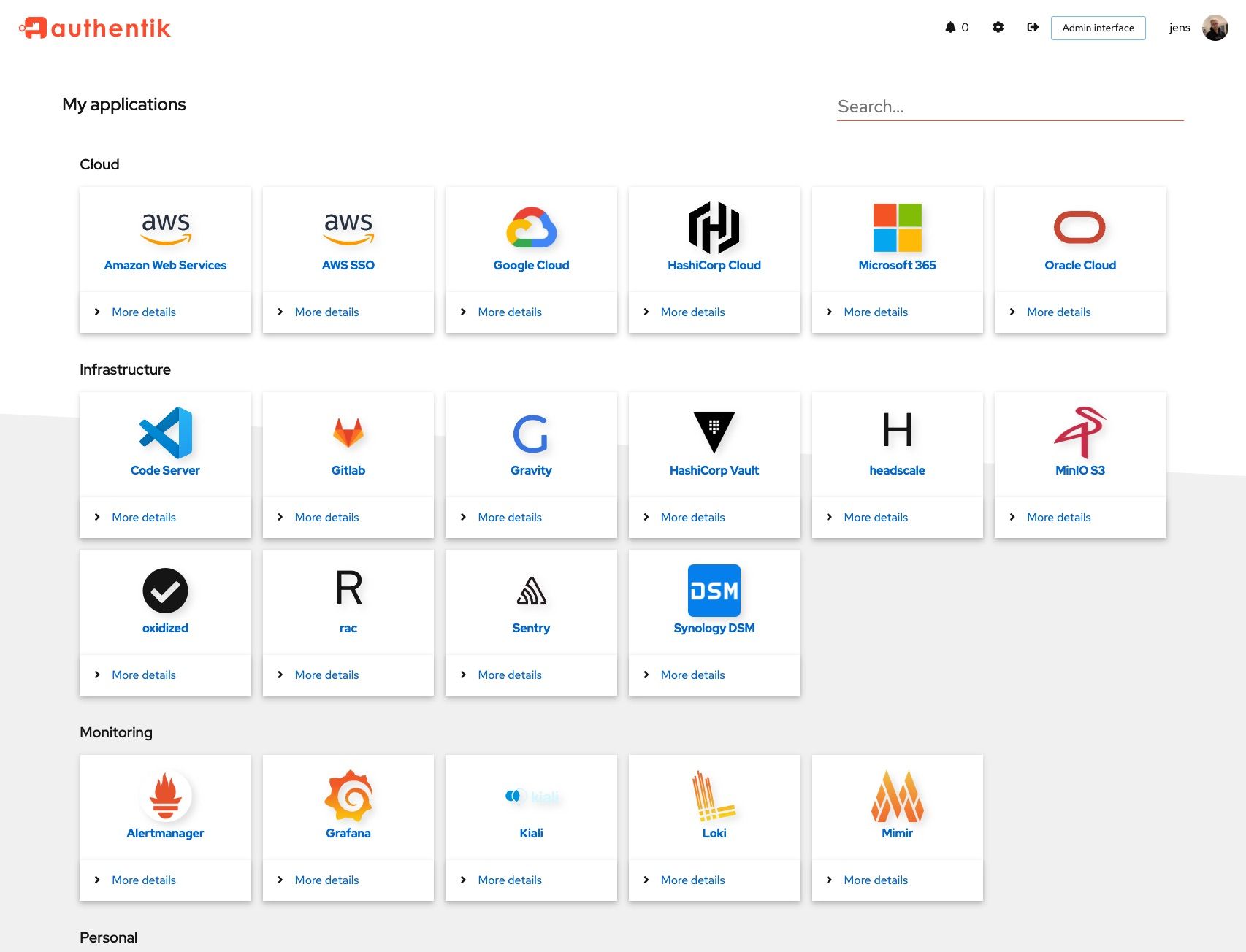 |
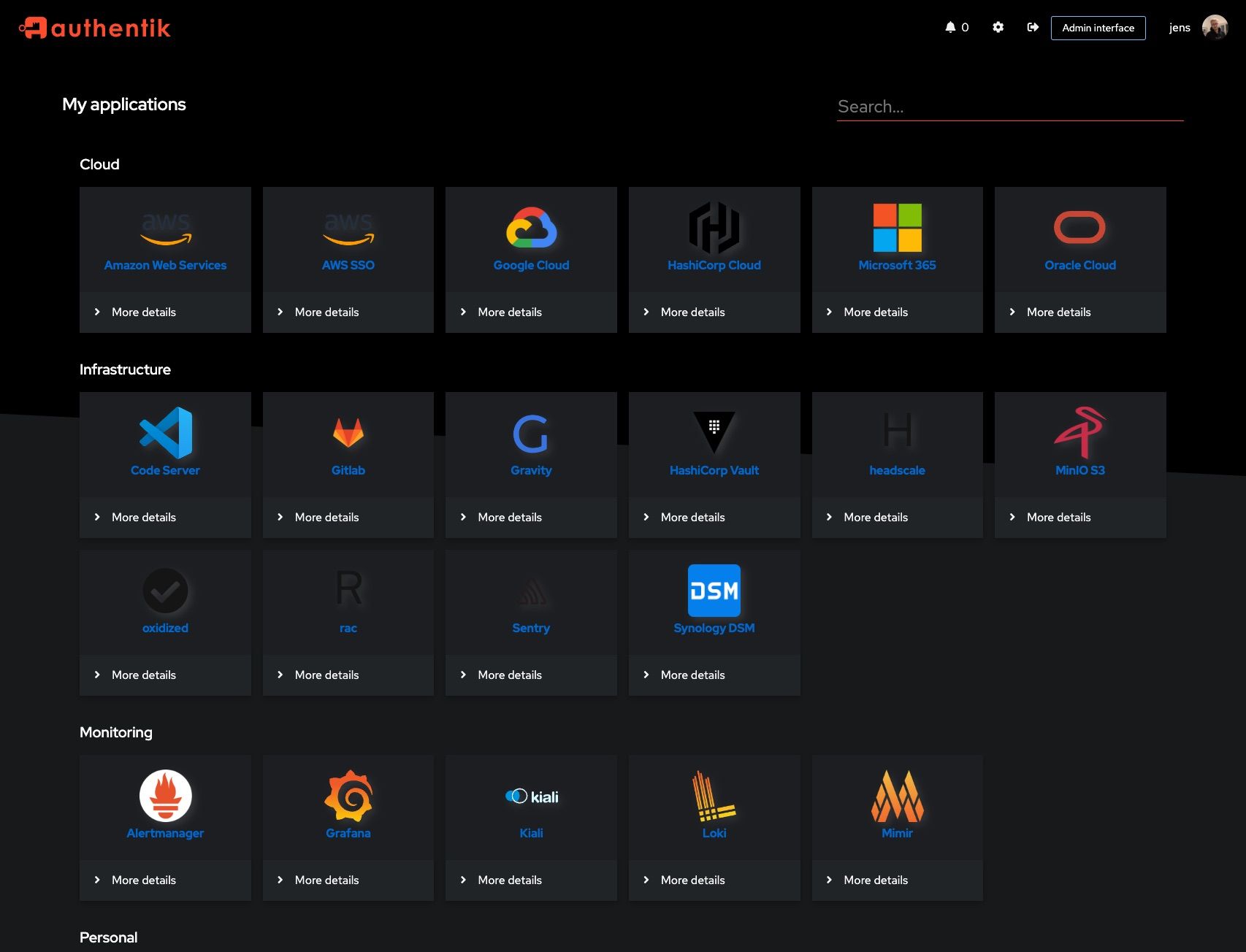 |
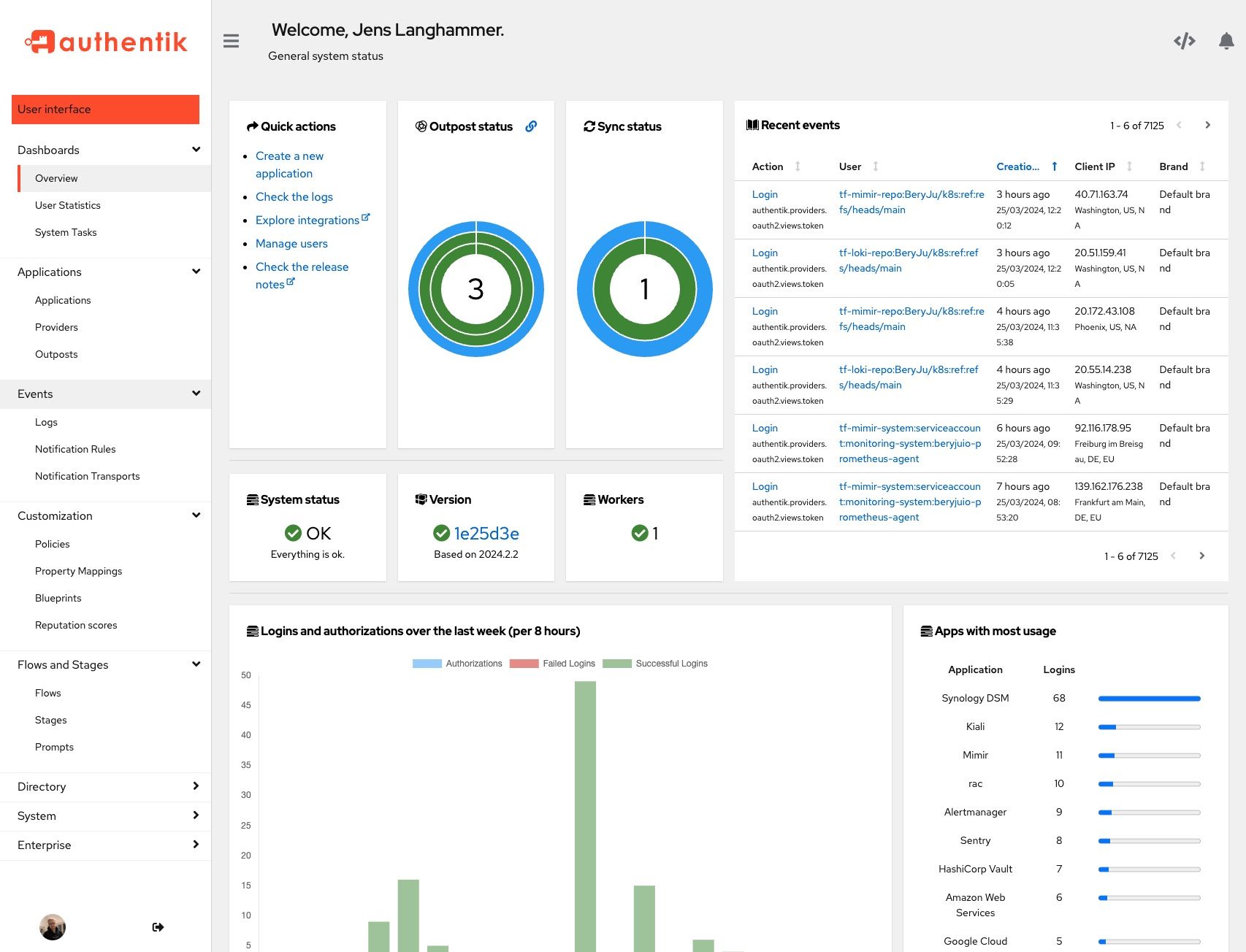 |
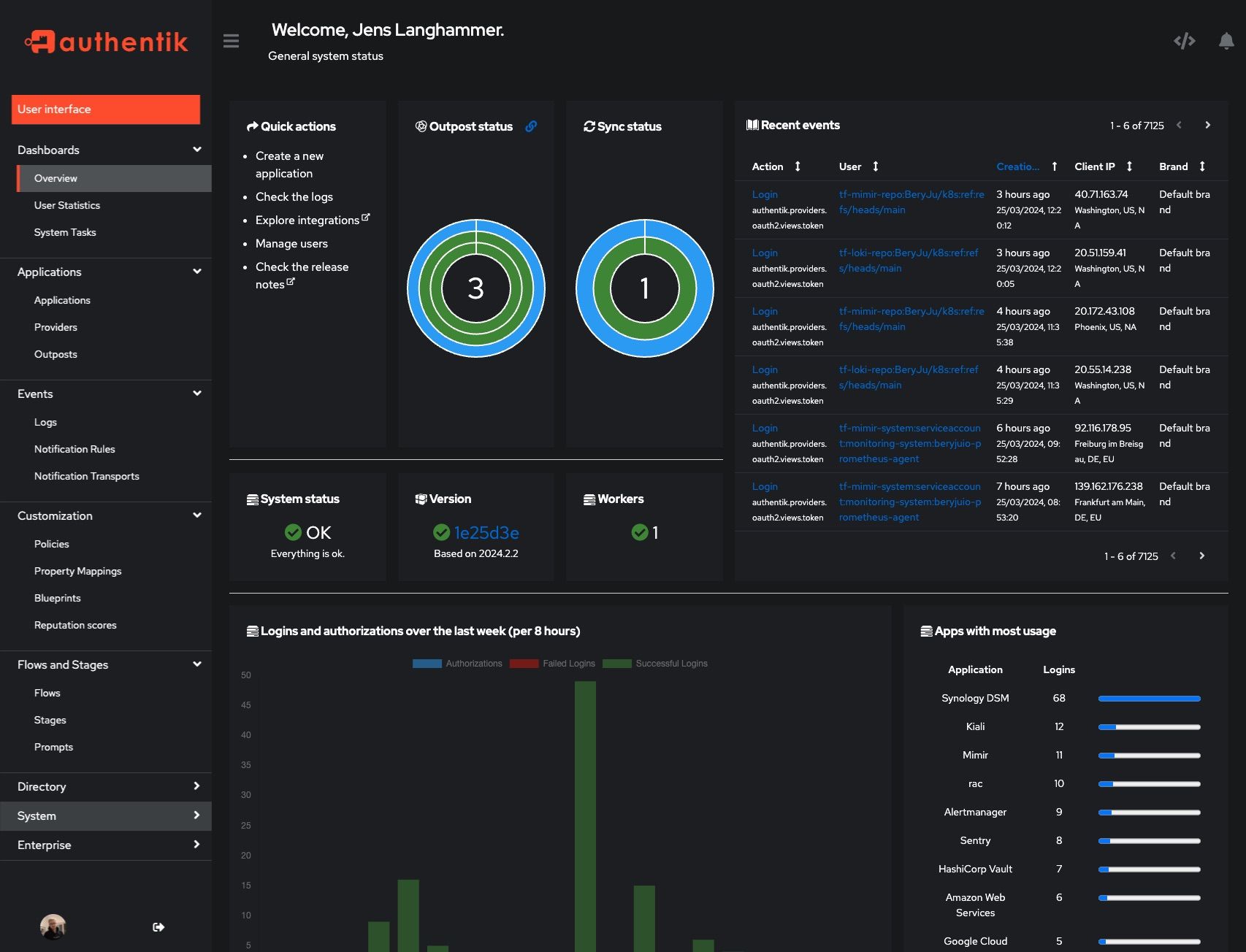 |
Development
Security
See SECURITY.md
Adoption and Contributions
Your organization uses authentik? We'd love to add your logo to the readme and our website! Email us @ hello@goauthentik.io or open a GitHub Issue/PR! For more information on how to contribute to authentik, please refer to our CONTRIBUTING.md file.
Description
The authentication glue you need.
authenticationauthentikauthorizationkubernetesoauth2oauth2-clientoauth2-serveroidcoidc-clientoidc-providerproxyreverse-proxysamlsaml-idpsaml-spsecuritysso
Readme
MIT
664 MiB
Languages
Python
51.7%
TypeScript
36.4%
MDX
5.1%
Go
3.7%
JavaScript
1.6%
Other
1.4%







